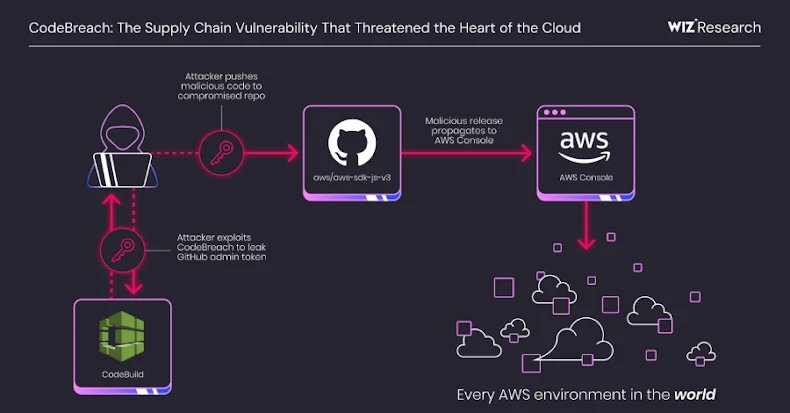

A vital misconfiguration in Amazon Internet Companies (AWS) CodeBuild might have allowed full takeover of the cloud service supplier’s personal GitHub repositories, together with its AWS JavaScript SDK, placing each AWS surroundings in danger.
The vulnerability has been codenamed CodeBreach by cloud safety firm Wiz. The problem was mounted by AWS in September 2025 following accountable disclosure on August 25, 2025.
“By exploiting CodeBreach, attackers might have injected malicious code to launch a platform-wide compromise, doubtlessly affecting not simply the numerous purposes relying on the SDK, however the Console itself, threatening each AWS account,” researchers Yuval Avrahami and Nir Ohfeld stated in a report shared with The Hacker Information.
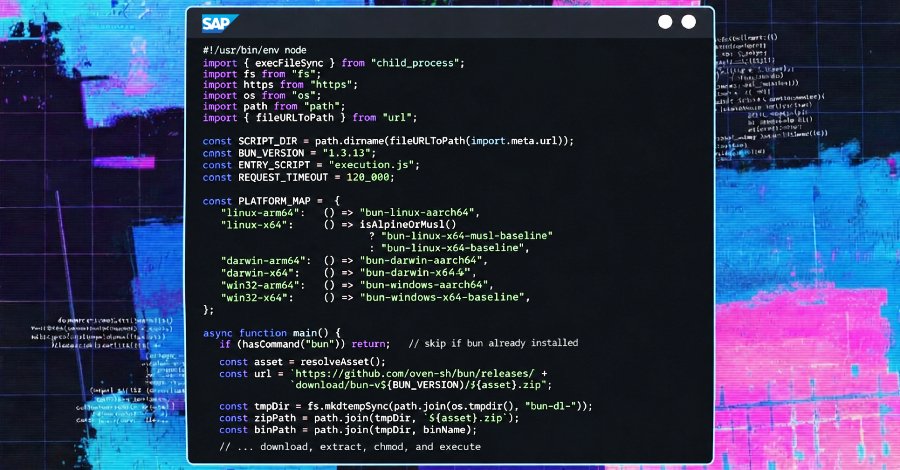
The flaw, Wiz famous, is the results of a weak point within the steady integration (CI) pipelines that would have enabled unauthenticated attackers to breach the construct surroundings, leak privileged credentials like GitHub admin tokens, after which use them to push malicious modifications to the compromised repository – making a pathway for provide chain assaults.
Put in another way, the difficulty undermines webhook filters launched by AWS to make sure that solely sure occasions set off a CI construct. For instance, AWS CodeBuild will be configured such {that a} construct is triggered solely when code modifications are dedicated to a selected department or when a GitHub or GitHub Enterprise Server account ID (aka ACTOR_ID or actor ID) matches the common expression sample. These filters serve to safe in opposition to untrusted pull requests.

The misconfiguration impacted the next AWS-managed open supply GitHub repositories, that are configured to run builds on pull requests –
- aws-sdk-js-v3
- aws-lc
- amazon-corretto-crypto-provider
- awslabs/open-data-registry
The 4 tasks, which applied an ACTOR_ID filter, suffered from a “deadly flaw” in that they failed to incorporate two characters to make sure – particularly the beginning ^ and finish $ anchors – essential to yield an actual common expression (regex) match. As a substitute, the regex sample allowed any GitHub person ID that was a superstring of an accepted ID (e.g., 755743) to bypass the filter and set off the construct.
As a result of GitHub assigns numeric person IDs sequentially, Wiz stated it was in a position to predict that the brand new person IDs (presently 9-digits lengthy) would “eclipse” a trusted maintainer’s six-digit ID roughly each 5 days. This perception, coupled with the usage of GitHub Apps to automate app creation (which, in flip, creates a corresponding bot person), made it doable to generate a goal ID (e.g., 226755743) by triggering tons of of latest bot person registrations.
Armed with the actor ID, an attacker can now set off a construct and procure the GitHub credentials of the aws-sdk-js-v3 CodeBuild venture, a Private Entry Token (PAT) belonging to the aws-sdk-js-automation person, which has full admin privileges over the repository.

The attacker can weaponize this elevated entry to push code on to the primary department, approve pull requests, and exfiltrate repository secrets and techniques, ultimately setting the stage for provide chain assaults.
“The above repositories’ configured common expressions for AWS CodeBuild webhook filters meant to restrict trusted actor IDs had been inadequate, permitting a predictably acquired actor ID to achieve administrative permissions for the affected repositories,” AWS stated in an advisory launched right now.
“We are able to affirm these had been project-specific misconfigurations in webhook actor ID filters for these repositories and never a problem within the CodeBuild service itself.”
Amazon additionally stated it remediated the recognized points, together with implementing extra mitigations, equivalent to credential rotations and steps to safe the construct processes that comprise GitHub tokens or another credentials in reminiscence. It additional emphasised that it discovered no proof of CodeBreach having been exploited within the wild.
To mitigate such dangers, it is important that untrusted contributions doesn’t set off privileged CI/CD pipelines by enabling the brand new Pull Request Remark Approval construct gate, use CodeBuild-hosted runners to handle construct triggers by way of GitHub workflows, guarantee regex patterns in webhook filters are anchored, generate a novel PAT for every CodeBuild venture, restrict the PAT’s permissions to the minimal required, and think about using a devoted unprivileged GitHub account for CodeBuild integration.

“This vulnerability is a textbook instance of why adversaries goal CI/CD environments: a refined, simply ignored flaw that may be exploited for enormous influence,” Wiz researchers famous. “This mixture of complexity, untrusted information, and privileged credentials creates an ideal storm for high-impact breaches that require no prior entry.”
This isn’t the primary time CI/CD pipeline safety has attracted scrutiny. Final yr, analysis from Sysdig detailed how insecure GitHub Actions workflows related to the pull_request_target set off might be exploited to leak the privileged GITHUB_TOKEN and achieve unauthorized entry to dozens of open-source tasks through the use of a single pull request from a fork.
An identical two-part evaluation from Orca Safety discovered insecure pull_request_target in tasks from Google, Microsoft, NVIDIA, and different Fortune-500 firms that would have allowed attackers to run arbitrary code, exfiltrate delicate secrets and techniques, and push malicious code or dependencies to trusted branches. The phenomenon has been dubbed pull_request_nightmare.
“By abusing misconfigured workflows triggered by way of pull_request_target, adversaries might escalate from an untrusted forked pull request into distant code execution (RCE) on GitHub-hosted and even self-hosted runners,” safety researcher Roi Nisimi famous.
“GitHub Actions workflows that use the pull_request_target ought to by no means checkout untrusted code with out an acceptable validation. As soon as they do, they’re prone to a full compromise.”