Ravie LakshmananMight 02, 2026Information Breach / Enterprise Safety Cybersecurity firm Trellix has introduced that...
Security
A tough steadiness Erik Avakian, technical counselor at Information-Tech Analysis Group, famous that when...
Warnings about helpdesk impersonation scams and Iran-linked hackers concentrating on crucial sectors within the...
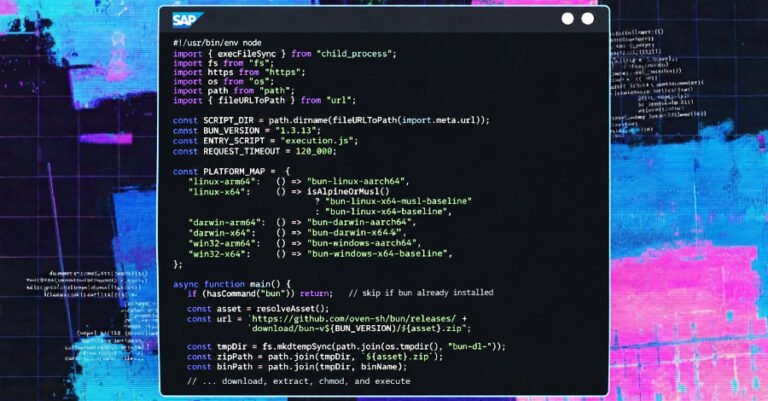
Ravie LakshmananApr 30, 2026Provide Chain Assault / Malware In one more software program provide...
The third potential goal that matched the principles, Modelo Hidrodinâmico (MOHID), is an open-source...
Ravie LakshmananApr 29, 2026Provide Chain Assault / Malware Cybersecurity researchers are sounding the alarm...
Third Social gathering Danger Administration hilft Unternehmen, das Risiko von Compliance-Verstößen zu vermeiden. Foto:...
Ravie LakshmananApr 28, 2026Vulnerability / Software program Safety Cybersecurity researchers have disclosed particulars of...
EDR-Software program verhindert Endpunkt-Sicherheitsdebakel. Die richtige Lösung vorausgesetzt. SvetaZi | shutterstock.com Software program im...
Ravie LakshmananApr 27, 2026 Checkmarx has disclosed that its ongoing investigation tied to the...