In one more software program provide chain assault, menace actors have managed to compromise the favored Python package deal Lightning to push two malicious variations to conduct credential theft.
In keeping with Aikido Safety, OX Safety, Socket, and StepSecurity, the 2 malicious variations are variations 2.6.2 and a couple of.6.3, each of which had been printed on April 30, 2026. The marketing campaign is assessed to be an extension of the Mini Shai-Hulud provide chain incident that focused SAP-related npm packages on Wednesday.
As of writing, the undertaking has been quarantined by the directors of the Python Package deal Index (PyPI) repository. PyTorch Lightning is an open-source Python framework that gives a high-level interface for PyTorch. The open-source undertaking has greater than 31,100 stars on GitHub.
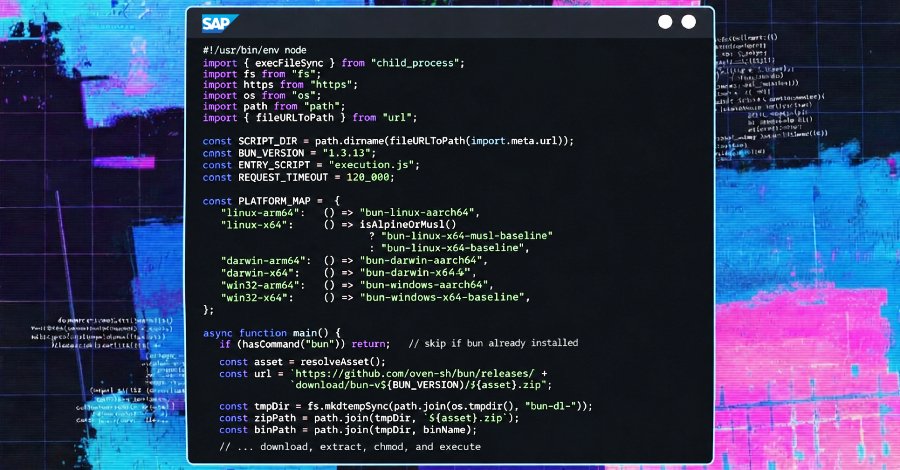
“The malicious package deal features a hidden _runtime listing containing a downloader and an obfuscated JavaScript payload,” Socket stated. “The execution chain runs routinely when the lightning module is imported, requiring no further consumer motion after set up and import.”
The assault chain paves the best way for a Python script (“begin.py”), which downloads and executes the Bun JavaScript runtime, after which makes use of it to run an 11MB obfuscated malicious payload (“router_runtime.js”) with an aimto conduct complete credential theft.
From among the many harvested credentials, the GitHub tokens are validated towards the “api.github[.]com/consumer” endpoint earlier than getting used to inject a worm-like payload to as much as 50 branches retrieved from each repository the token can write to.

“The operation is an upsert: it creates information that don’t but exist and silently overwrites information that do,” Socket added. “No pre-check for current content material is carried out. Each poisoned commit is authored utilizing a hardcoded id designed to impersonate Anthropic’s Claude Code.”
Individually, the malware implements an npm-based propagation vector that modifies the developer’s native npm packages with a postinstall hook within the “package deal.json” file to invoke the malicious payload, will increase the patch model quantity, and repacks the .tgz tarballs. Ought to the unsuspecting developer publish the tampered packages from their native setting, they’re made accessible on npm, from the place the malware finally ends up on downstream consumer programs.

The maintainers of the undertaking have acknowledged that “we’re conscious of the difficulty and are actively investigating.” It is at the moment not clear how the incident occurred, however indications are that the undertaking’s GitHub account has been compromised.
In a separate advisory, Lightning revealed an investigation remains to be underway to find out the precise root reason behind the compromise and that the “affected variations have launched performance in step with a credential harvesting mechanism.”
Within the interim, it is suggested to dam Lightning variations 2.6.2 and a couple of.6.3 and take away them from developer programs, if already put in. It is also important to downgrade to the final recognized clear model, 2.6.1, and rotate credentials uncovered in affected environments.
The availability chain assault is the most recent addition to an extended checklist of compromises carried out by a menace actor referred to as TeamPCP, which has now launched an onion web site on the darkish net after its account was suspended from X for violating the platform’s guidelines.
It additionally known as LAPSUS$, a “good companion of ours and has been concerned closely all through this whole operation.” The group additionally made it a degree to emphasise that it has “by no means used VECT encryption instruments and we personal CipherForce, our personal personal locker,” following a report from Examine Level Analysis about vulnerabilities found within the ransomware’s encryption course of.
Intercom npm Package deal Compromised as A part of Mini Shai-Hulud
In a associated growth, it has emerged that model 7.0.4 of intercom-client has been compromised as a part of the Mini Shai-Hulud marketing campaign, following the same modus operandi as that of the SAP packages to set off the execution of a credential-stealing malware utilizing a preinstall hook.
“The overlap is important as a result of the SAP CAP marketing campaign was linked to TeamPCP exercise primarily based on shared technical particulars, together with distinctive payload implementation patterns, GitHub-based exfiltration, credential harvesting throughout developer and CI/CD environments, and similarities to prior assaults affecting Checkmarx, Bitwarden, Telnyx, LiteLLM, and Aqua Safety Trivy,” Socket stated.