Jan 17, 2026Ravie LakshmananSynthetic Intelligence / Knowledge Privateness OpenAI on Friday mentioned it might...
Security
In keeping with Cisco, this function is just not enabled by default, and, it...
Is your group’s senior management susceptible to a cyber-harpooning? Discover ways to preserve them...
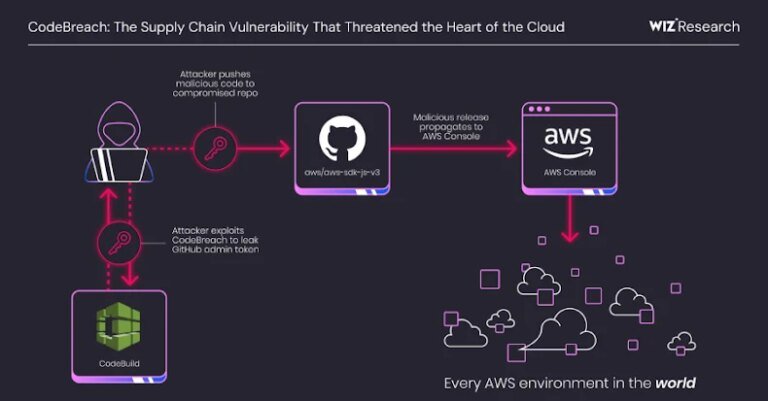
A vital misconfiguration in Amazon Internet Companies (AWS) CodeBuild might have allowed full takeover...
srcset=”https://b2b-contenthub.com/wp-content/uploads/2026/01/shutterstock_2701236855.jpg?high quality=50&strip=all 5234w, https://b2b-contenthub.com/wp-content/uploads/2026/01/shutterstock_2701236855.jpg?resize=300percent2C168&high quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2026/01/shutterstock_2701236855.jpg?resize=768percent2C432&high quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2026/01/shutterstock_2701236855.jpg?resize=1024percent2C576&high quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2026/01/shutterstock_2701236855.jpg?resize=1536percent2C864&high quality=50&strip=all...
Deciphering the huge cybersecurity vendor panorama by the lens of trade analysts and testing...
Jan 14, 2026Ravie LakshmananSoftware Safety / Vulnerability Node.js has launched updates to repair what...
Whereas AI continues to dominate the cybersecurity panorama, a number of different applied sciences...
Being seen as dependable is sweet for ‘enterprise’ and ransomware teams care about ‘model...
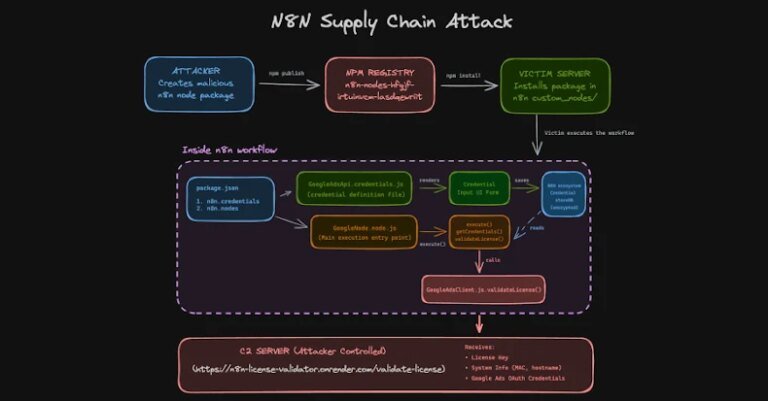
Jan 12, 2026Ravie LakshmananVulnerability / Workflow Automation Risk actors have been noticed importing a...