
A brand new marketing campaign has leveraged the ClickFix social engineering tactic as a approach to distribute a beforehand undocumented malware loader known as DeepLoad.
“It possible makes use of AI-assisted obfuscation and course of injection to evade static scanning, whereas credential theft begins instantly and captures passwords and classes even when the first loader is blocked,” ReliaQuest researchers Thassanai McCabe and Andrew Currie stated in a report shared with The Hacker Information.
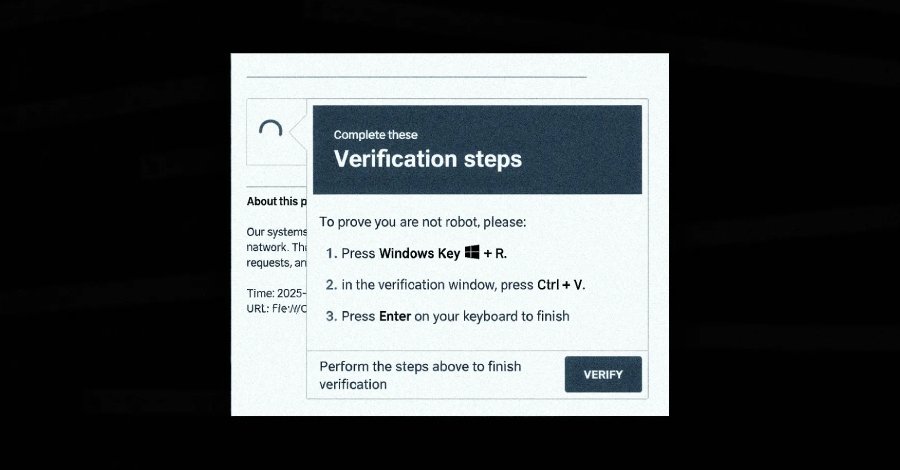
The place to begin of the assault chain is a ClickFix lure that tips customers into operating PowerShell instructions by pasting the command into the Home windows Run dialog beneath the pretext of addressing a non-existent situation. This, in flip, makes use of “mshta.exe,” a official Home windows utility to obtain and run an obfuscated PowerShell loader.
The loader, for its half, has been discovered to hide its precise performance amongst meaningless variable assignments, possible in an try to deceive safety instruments. It is assessed that the menace actors relied on a synthetic intelligence (AI) instrument to develop the obfuscation layer.
DeepLoad makes deliberate efforts to mix in with common Home windows exercise and fly beneath the radar. This contains hiding the payload inside an executable named “LockAppHost.exe,” a official Home windows course of that manages the lock display screen.
As well as, the malware covers up its personal tracks by disabling PowerShell command historical past and invoking native Home windows core features instantly as an alternative of counting on PowerShell’s built-in instructions to launch processes and modify reminiscence. In doing so, it bypasses frequent monitoring hooks that maintain tabs on PowerShell-based exercise.
“To evade file-based detection, DeepLoad generates a secondary part on the fly by utilizing the built-in PowerShell characteristic Add-Kind, which compiles and runs code written in C#,” ReliaQuest stated. “This produces a brief Dynamic Hyperlink Library (DLL) file dropped into the person’s Temp listing.”
This affords a method for the malware to sidestep file name-based detections, because the DLL is compiled each time it is executed and written with a randomized file identify.
One other notable protection evasion tactic adopted by DeepLoad is using asynchronous process name (APC) injection to run the principle payload inside a trusted Home windows course of and not using a decoded payload written to disk after launching the goal course of in a suspended state, writing shellcode into its reminiscence, after which resuming the execution of the method.
DeepLoad is designed to facilitate credential theft by extracting browser passwords from the host. It additionally drops a malicious browser extension that intercepts credentials as they’re being entered on login pages and persists throughout person classes except it is explicitly eliminated.
A extra harmful characteristic of the malware is its capacity to robotically detect when detachable media gadgets like USB drives are related and duplicate the malware-laced recordsdata utilizing names like “ChromeSetup.lnk,” “Firefox Installer.lnk,” and “AnyDesk.lnk” in order to set off the an infection as soon as it is doubled-clicked.
“DeepLoad used Home windows Administration Instrumentation (WMI) to reinfect a ‘clear’ host three days later with no person motion and no attacker interplay,” ReliaQuest defined. “WMI served two functions: It broke the parent-child course of chains most detection guidelines are constructed to catch, and it created a WMI occasion subscription that quietly re-executed the assault later.”
The purpose, it seems, is to deploy multi-purpose malware that may carry out malicious actions throughout the cyber kill chain and sidestep detection by safety controls by avoiding writing artifacts to disk, mixing into Home windows processes, and spreading rapidly to different machines.
The disclosure comes as G DATA detailed one other malware loader dubbed Kiss Loader that is distributed by means of Home windows Web Shortcut recordsdata (URL) hooked up to phishing emails, which then connects to a distant WebDAV useful resource hosted on a TryCloudflare area to serve a secondary shortcut that masquerades as a PDF doc.
As soon as executed, the shortcut launches a WSH script chargeable for operating a JavaScript part, which proceeds to retrieve and execute a batch script that shows a decoy PDF, units up persistence within the Startup folder, and downloads the Python-based Kiss Loader. Within the closing stage, the loader decrypts and runs Venom RAT, an AsyncRAT variant, utilizing APC injection.
It is presently not recognized how widespread assaults deploying Kiss Loader are, and if it is being supplied beneath a malware-as-a-service (MaaS) mannequin. That stated, the menace actor behind the loader claims to be from Malawi.







