
The Russia-linked risk actor identified as APT28 (aka Forest Blizzard) has been linked to a brand new marketing campaign that has compromised insecure MikroTik and TP-Hyperlink routers and modified their settings to show them into malicious infrastructure beneath their management as a part of a cyber espionage marketing campaign since at the very least Might 2025.
The massive-scale exploitation marketing campaign has been codenamed FrostArmada by Lumen’s Black Lotus Labs, with Microsoft describing it as an effort to use weak dwelling and small workplace (SOHO) web units to hijack DNS visitors and allow passive assortment of community information.
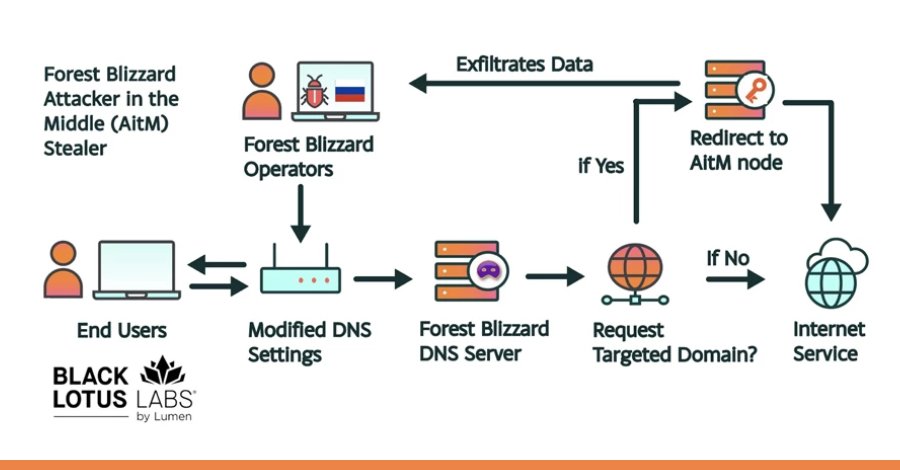
“Their approach modified DNS settings on compromised routers to hijack native community visitors to seize and exfiltrate authentication credentials,” Black Lotus Labs stated in a report shared with The Hacker Information.
“When focused domains had been requested by a consumer, the actor redirected visitors to an attacker-in-the-middle (AitM) node, the place these credentials had been harvested and exfiltrated. This method enabled a virtually invisible assault that required no interplay from the top consumer.”
The infrastructure related to the marketing campaign has been disrupted and brought offline as a part of a joint operation in collaboration with the U.S. Division of Justice, Federal Bureau of Investigation, and different worldwide companions.
The exercise is assessed to have commenced way back to Might 2025 in a restricted capability, adopted by widespread router exploitation and DNS redirection commencing in early August. At its peak in December 2025, greater than 18,000 distinctive IP addresses from at least 120 international locations had been discovered speaking with APT28 infrastructure.
These efforts primarily singled out authorities companies, akin to ministries of international affairs, regulation enforcement, and third-party e mail and cloud service suppliers throughout North African, Central American, Southeast Asian, and European international locations.
The Microsoft Menace Intelligence crew, in its evaluation of the marketing campaign, attributed the exercise to APT28 and its sub-group tracked as Storm-2754. The tech large stated it recognized greater than 200 organizations and 5,000 client units impacted by the risk actor’s malicious DNS infrastructure.
“For nation-state actors like Forest Blizzard, DNS hijacking allows persistent, passive visibility and reconnaissance at scale,” Redmond stated. “By compromising edge units which can be upstream of bigger targets, risk actors can reap the benefits of much less intently monitored or managed property to pivot into enterprise environments.”

The DNS hijacking exercise has additionally facilitated AitM assaults that made it attainable to facilitate the theft of passwords, OAuth tokens, and different credentials for net and email-related companies, placing organizations liable to broader compromise.
The event marks the primary time the adversarial collective has been noticed utilizing DNS hijacking at scale to assist AiTM of Transport Layer Safety (TLS) connections after exploiting edge units, Microsoft added.
At a excessive degree, the assault chain entails APT28 gaining distant administrative entry to SOHO units and altering default community configurations to make use of DNS resolvers beneath its management. The malicious reconfiguration causes the units to ship their DNS requests to actor-controlled servers.
This, in flip, causes DNS lookups for e mail functions or login pages to be resolved by the malicious DNS server. The risk actor then makes an attempt to conduct AitM assaults towards these connections to steal consumer account credentials by tricking the victims into connecting to malicious infrastructure.
A few of these domains are related to Microsoft Outlook on the net. Microsoft stated it additionally recognized AitM exercise aimed toward non-Microsoft hosted servers in at the very least three authorities organizations in Africa.
“It’s believed that the DNS hijacking operations are opportunistic in nature, with the actor gaining visibility of a giant pool of candidate goal customers then filtering down customers at every stage within the exploitation chain to triage for victims of possible intelligence worth,” the U.Ok. Nationwide Cyber Safety Centre (NCSC) stated.
APT28 is claimed to have exploited TP-Hyperlink WR841N routers for its DNS poisoning operations by possible taking benefit of CVE-2023-50224 (CVSS rating: 6.5), an authentication bypass vulnerability that might be used to extract saved credentials through specifically crafted HTTP GET requests.
A second cluster of servers has been discovered to obtain DNS requests through compromised routers and subsequently ahead them to distant actor-owned servers. This cluster can also be assessed to have engaged in interactive operations focusing on a small variety of MikroTik routers situated in Ukraine.
“Forest Blizzard’s DNS hijacking and AitM exercise permits the actor to conduct DNS assortment on delicate organizations worldwide and is in step with the actor’s longstanding remit to gather espionage towards precedence intelligence targets,” Microsoft stated.
“Though we now have solely noticed Forest Blizzard using their DNS hijacking marketing campaign for info assortment, an attacker might use an AiTM place for added outcomes, akin to malware deployment or denial of service.”







